Ten Key Reasons for Implementing Secure Cloud Development Environments in Enterprises
In the rapidly evolving digital landscape, data security when developing in the Cloud has emerged as a cornerstone for enterprises across the globe. Here, we delve into the top ten reasons why enabling data security when working with Cloud-based environments such as online containers is paramount for the enterprise market.
As organizations navigate through vast amounts of sensitive data, safeguarding this digital asset becomes not just a necessity but a strategic imperative. For that purpose the use of Cloud Development Environments with embedded security, i.e. Secure Cloud Development Environments, is a critical component to achieve secure software development, i.e. security around all the development assets used across the DevOps process.
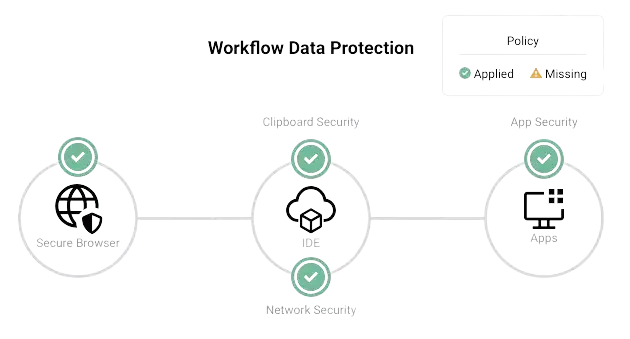
The use of secure Cloud Development Environments (CDEs) is also an ideal way to implement and automate Enterprise DevSecOps strategies and put in place secure software development best-practices due to the control that organizations achieve on their development workflow thanks to secure CDEs. Strong Network provides the first platform to manage secure Cloud Development Environments in the Enterprise market. By using it, organizations achieve unmatched asset security, in particular source code protection, application and service credentials protection, and general protection against data exfiltration with the most advanced Data Loss Prevention mechanism for Cloud Development Environments.
1. Protection of Sensitive Information
Enterprises often handle an array of sensitive data, including customer details, financial records, and trade secrets. This data, if compromised, can have catastrophic implications. Implementing robust data security measures is paramount to prevent unauthorized access and ensure the confidentiality and integrity of this sensitive information.
With data breaches on the rise, regulatory bodies worldwide have tightened their data protection laws. Regulations like GDPR, HIPAA, and PCI-DSS mandate stringent data security protocols. Non-compliance not only leads to hefty fines but can also invite legal complications, making compliance a critical aspect of enterprise data security.
3. Maintaining Customer Trust and Brand Reputation
In the digital age, customer trust is a valuable currency. Data breaches can severely tarnish an enterprise's reputation, leading to loss of customer trust and loyalty. Prioritizing data security helps maintain a positive brand image and assures customers that their data is in safe hands.
4. Preventing Financial Losses
The financial repercussions of a data breach are significant, encompassing breach mitigation costs, legal fees, and potential compensatory payments. Moreover, a breach can result in business losses and a decline in shareholder value. Investing in data security is, therefore, a prudent financial decision for enterprises.
5. Mitigating Cyber Threats
The cyber threat landscape is ever-evolving, with sophisticated threats like ransomware and phishing attacks posing constant challenges. Robust data security protocols act as a bulwark against these threats, protecting enterprise data from malicious actors.
6. Enabling Digital Transformation
Digital transformation has become a strategic initiative for many enterprises. This transformation, however, expands the attack surface. Data security ensures that embracing cloud services, big data, and IoT technologies does not compromise data integrity and confidentiality.
7. Supporting Remote Work and Mobility
The shift towards remote work and a mobile workforce necessitates secure access to data from various locations and devices. Data security measures ensure that this flexibility does not become a liability, safeguarding data regardless of where or how it is accessed.
8. Intellectual Property Protection
For many enterprises, intellectual property (IP) is a critical asset. Protecting this IP from theft or espionage is crucial to maintaining a competitive edge and fostering innovation. Effective data security measures are essential to safeguard these invaluable assets.
9. Global Business Operations
With enterprises operating in multiple jurisdictions, each with its unique data protection laws, comprehensive data security becomes imperative. It not only ensures compliance across borders but also instills confidence in international clients and partners.
10. Business Continuity and Resilience
In the event of a cyberattack or data breach, the ability to continue operations is crucial. Data security is a key component of business continuity planning, ensuring minimal disruption and quick recovery from any security incidents.
In conclusion, data security in the enterprise market is not merely about compliance or risk mitigation; it's a strategic business decision that underpins all aspects of modern enterprise operations. From protecting sensitive information and maintaining customer trust to enabling digital transformation and safeguarding intellectual property, the role of data security is all-encompassing. As enterprises continue to navigate the complex digital ecosystem, prioritizing data security will be pivotal to their success and sustainability. It's an investment that not only safeguards against immediate threats but also lays the foundation for a secure, resilient, and prosperous future in the digital world.
All material in this text can be shared and cited with appropriate credits. For more information about our platform, please contact us at hello@strong.network